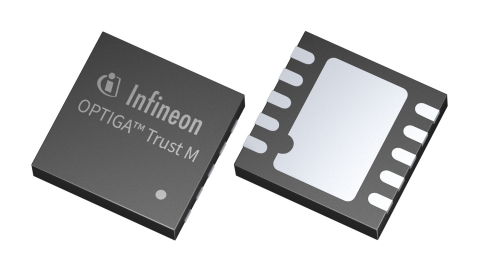
OPTIGA™ Trust M The easiest way to add security to your existing IoT designs
Overview
OPTIGA™ Trust M is a security solution with tamper-resistant hardware certified to Common Criteria EAL6+. The Secure Element can be used with any MCU/MPU or application processor to perform various security-related tasks autonomously and thus enhance the security of existing IoT designs. It is available with the OPTIGA™ Trust M MTR service supporting late-stage Matter provisioning and Infineon’s OPTIGA™ Trust M Express cloud provisioning service.
Summary of Features
- CC EAL6+ (high) certification
- ECC NIST curves up to P-521
- ECC Brainpool r1 curves up to P-512
- RSA up to 2048
- AES up to 256, HMAC up to SHA-512
- TLS v1.2 PRF and HKDF up to SHA-512
- TRNG/DRNG, 4 monotonic counters
- Up to 10 kB user memory
- I2C interface-shielded connection
- Hibernate mode for 0 power consump.
- USON-10 package (3 x 3 mm)
- Temperature range: -40 to + 105°C
- Lifetime: 20 years for Industrial
- Config. device security monitor
- Protected updates
Benefits
- Easiest way to add security
- Works with any MCU/MPU
- Robust, future-proof security
- Easy integration
- NDA-free product documentation
- MIT-licensed public host software
Complementary Products
Videos
Training
Applications
Support